News Releases
News Releases by SyncDog, the leading independent software vendor for containerized application security for enterprise mobile computing & mobile device management.
In the News
SyncDog Receives Prestigious NVTC Cyber50 Award for Its Groundbreaking Mobile Security Solution
Reston, VA -- SyncDog, a leading software company specializing in mobile security solutions, has been honored with the Northern Virginia Technology Council’s (NVTC) esteemed Cyber50 award. This recognition underscores SyncDog's significant contributions to the mobile...
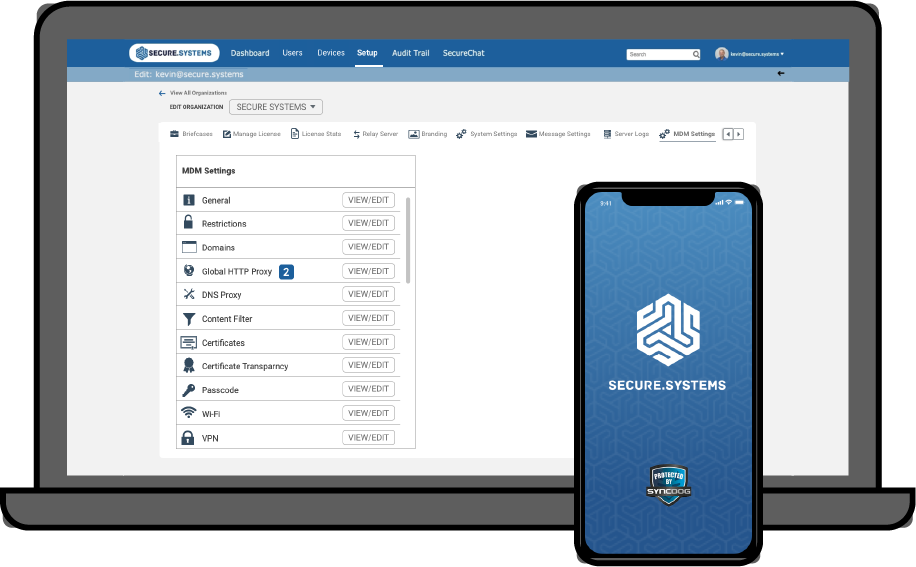
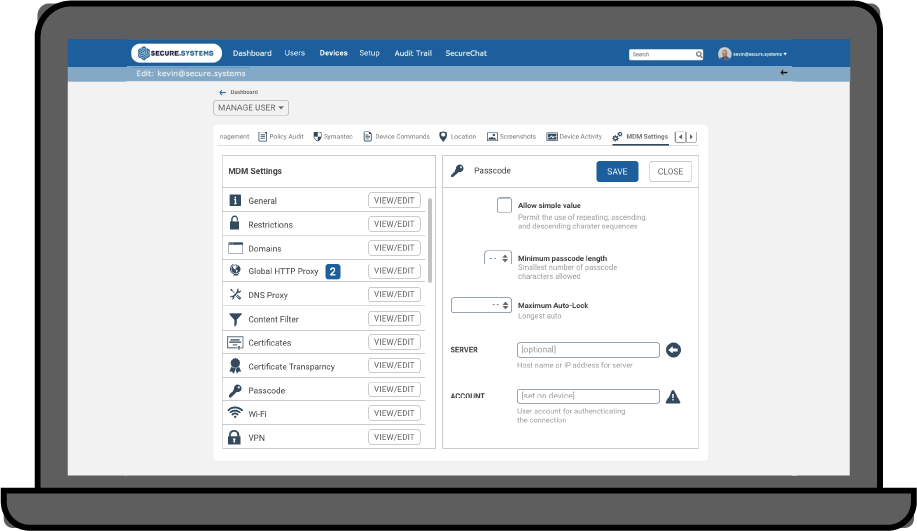
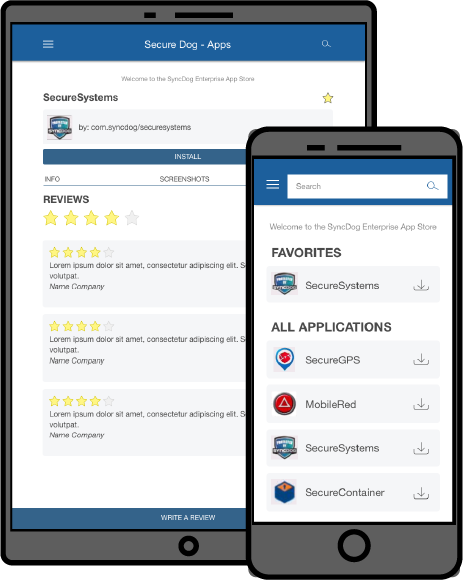
SyncDog Unveils First Fully Integrated Solution for Mobile Endpoint Security
Secure.Systems enables employees to work from anywhere within zero trust architectures by managing and protecting data, employees, and devices RESTON, Va., March 11, 2021 - SyncDog Inc., the leading Independent Software Vendor (ISV) for next generation mobile endpoint...
SyncDog Partners With Halodata To Advance Secure.Systems Across Southeast Asia
Distribution Agreement to Empower Region Ensuring Protection of Corporate Data on Employee's Mobile Devices RESTON, Va., Sept. 23, 2020 -- SyncDog, Inc., the leading Independent Software Vendor (ISV) for next generation mobile security and data loss prevention, today...
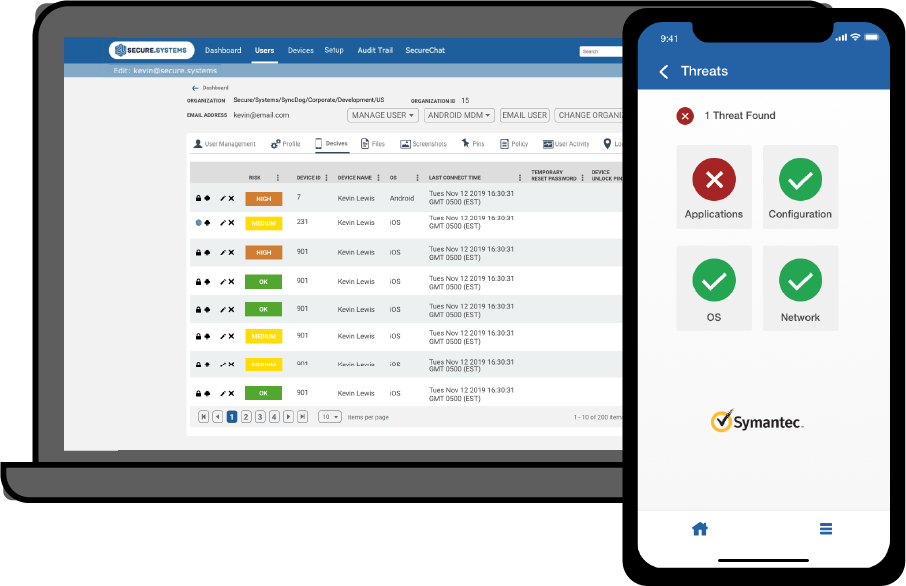
SyncDog Enhances Mobile Threat Defense Capabilities with Zimperium
On-Device Protection Detects Threats Targeting Mobile Devices in Real-Time RESTON, Va., July 22, 2020 -- SyncDog Inc., the leading Independent Software Vendor (ISV) for next generation mobile security and data loss prevention, today announced a partnership with...
Recent Blogs
SyncDog: Modern Mobile Security for FINRA Compliance
As financial institutions adopt Bring‑Your‑Own‑Device (BYOD) and Choose‑Your‑Own‑Device (COPE) models, FINRAregulations demand strict controls over data security, communication monitoring, auditability, and record retention. Traditional Mobile Device Management (MDM)...
The NFL Needs a 12th Man on Defense: SyncDog
Stolen Playbook iPad Sparks Security Concerns for National Football League (NFL) Teams In a recent unsettling event, Los Angeles Rams offensive lineman Conor McDermott found himself at the center of a possible security breach when his iPad, containing vital team...
VPN’s Create a Significant Security Gap
VPN solutions are one of the most common ways that organizations enable edge devices to access internal networks, files and data. But the latest CISA advisory highlights critical vulnerabilities in VPNs, particularly those exploited by China-sponsored cyberattacks....
What’s the Russian word for Privacy ? – There is None !
The concept of privacy is deeply embedded in Western democratic cultures, where individuals often expect a certain degree of personal autonomy and protection from the government or other authorities. However, this is not a universal norm, as reflected in language...
Contact Us
Take control of your Enterprise Mobile Security. Get started with a free 30 day trial with us.