Requirements for Full Mobile Endpoint Security
We Now Live in a Mobile Economy
With all the recent press around top government officials, notable company executives and many, many others having their mobile devices attacked – exposing all sensitive email, files, and apps – how can anyone feel safe using a mobile device for work? The simple answer is that unless your current mobile security solution is capable of addressing the newer, more advanced threats that are built to jailbreak/root the device – you are vulnerable. The scary part is that just about every solution on the market fails to prevent these newer, more advanced threats.
Mobile based attacks such as Pegasus, Predator and other such “Zero Day” threats continue to make headlines because of their ability to easily get around MDM/MAM based security architectures and access the device’s crypto Keystore – giving them full access to all emails, apps and data on the device. Man-in-the-middle attacks, non-persistent jailbreaks, SSL stripping and other types of attacks are all too much for MDM based solutions like Intune, AirWatch, ManageEngine etc. to handle. Here are a few examples from just this year:
· Apple Patches Actively Exploited WebKit Zero Day
· CISA Orders Agencies to Mitigate VMWare Vulnerabilities Under Deadline
True mobile security needs to incorporate a containerization-based solution that isolates and encrypts the data being accessed and stored on the device – and doesn’t rely on the keystore for storing it’s crypto. Challenge any vendor with this mobile security requirements list below before committing to any solution.
Requirements for full Mobile Endpoint Security
· Full encryption of data on the device and Full encryption of Data being sent or received from the device using AES 256-bit encryption at a minimum
· Containerized and encrypted isolation of all work-related emails, files, and apps from personal use (Android for Work does not comply)
· Encrypted transfer of data between apps on the device (Copy & Paste should be allowed between work related apps)
· Zero use of KeyStore for Crypto key storage
· Detection AND Response to non-persistent jailbreaks, Man-in-the-Middle, SSL Stripping and other Zero-Day type attacks
· Mobile Threat Defense (MTD) monitoring of device
· Support for BYOD without the use of a management profile to comply to many of the new data security/privacy regulations
SyncDog is the only solution on the market that offers a full end-to-end mobile endpoint security solution which addresses all the key components above.
Container-Encrypted Security
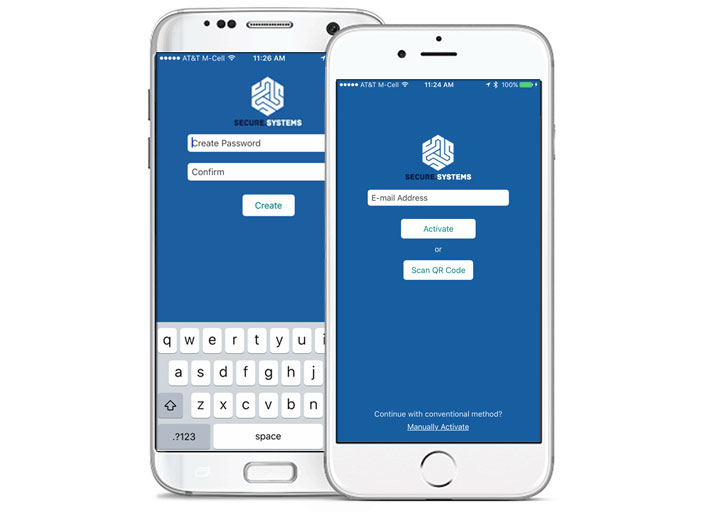
Secure.Systems™ stores emails, contacts, calendars, notes, tasks, documents and the intranet on a smartphone or tablet (iOS and Android™) in a secure, encrypted Container area.
Simple, Easy Management
Administrators, employees and compliance managers all benefit from the easy management of Secure.Systems™. Privileged users can easily define the security rules within the app and also grant or deny corporate data access privileges on devices. If an employee leaves the company or a device is lost or stolen, corporate data inside the Secure.Systems™ container can be remotely erased without infringing upon the employee’s personal data.
